A really really long list (in no particular order) of training materials, CTFs and websites to test your skills. Hacksplaining: Security Training for Developers Hack real, vulnerable web applications
Tag: security
Objective: Gain access to digital assets (ie: pdf) for free and check how well PII data is protected for a given website Disclaimer: I got permission to perform the
Have you ever wanted to become a hacker or to experience the thrill when you gain root access on a government vulnerable server? I always thought security was the
Run a CTF event using CTFd - import and export challenges in a portable, human-readable format (YAML).
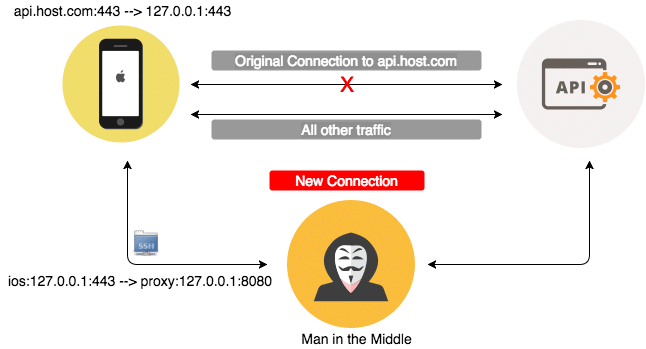
This tutorial will describe how you can use the MitM attack to alter the default behaviour of a mobile application. As result, the application will return all its remote